Patch Management That Prevents Business Downtime
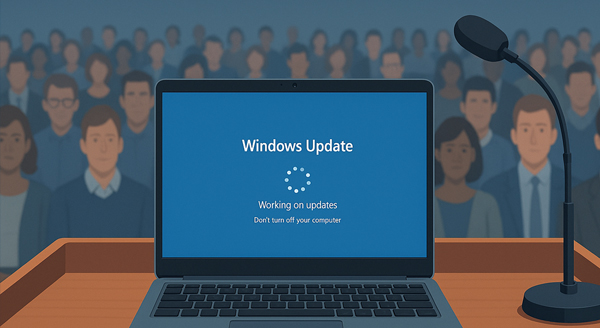
Patch Management prevents those stressful moments when your laptop decides to update right before a big client meeting. You fire up your device in the lobby, slides polished and demo ready, feeling calm and prepared. Then Windows or macOS suddenly installs dozens of updates, leaving you staring at a spinning [...]